Key Features
User Authorization ManagementSAP Authorization Summary
- T-Code usage rate by user
- Detection of users violating basic security policies
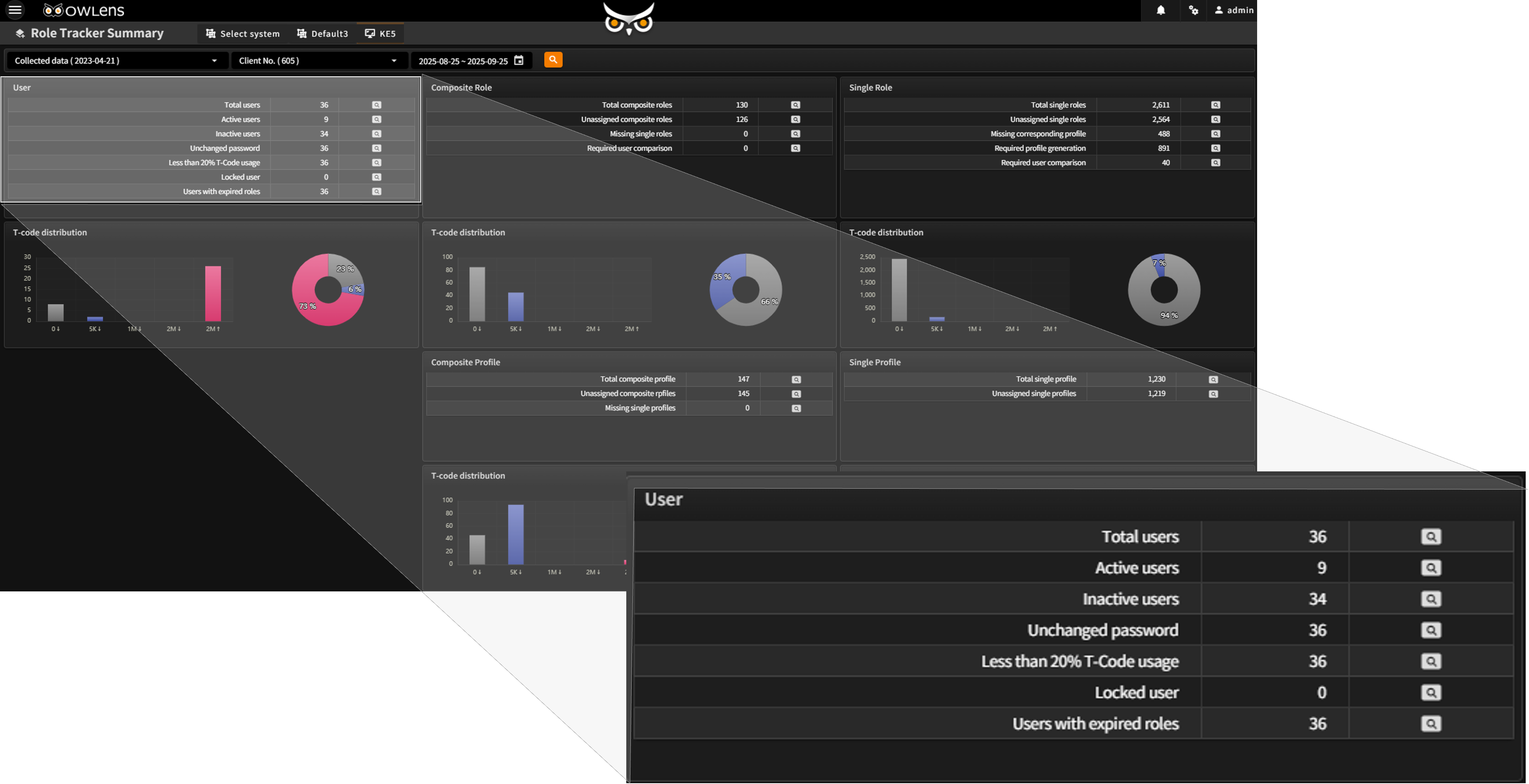
User
- Users who have not logged in
- Users who have not changed their password
- Users with less than 10% transaction usage rate
- Users with duplicate logins
- Locked users
- Users assigned to expired roles
Role
- Roles not assigned to any user
- Composite roles that do not contain single roles
- Roles without profiles
- Roles requiring user comparison
Profile
- Profiles not assigned to any user
- Composite profiles that do not contain single profiles
- Search by various conditions for User, Role, Profile, and T-Code
- Intuitive visualization of relationships between authorization objects through tree view
Flexible Search Conditions
- Focused search on objects of interest
Authorization Data History Management
- Easily track change history of authorization settings
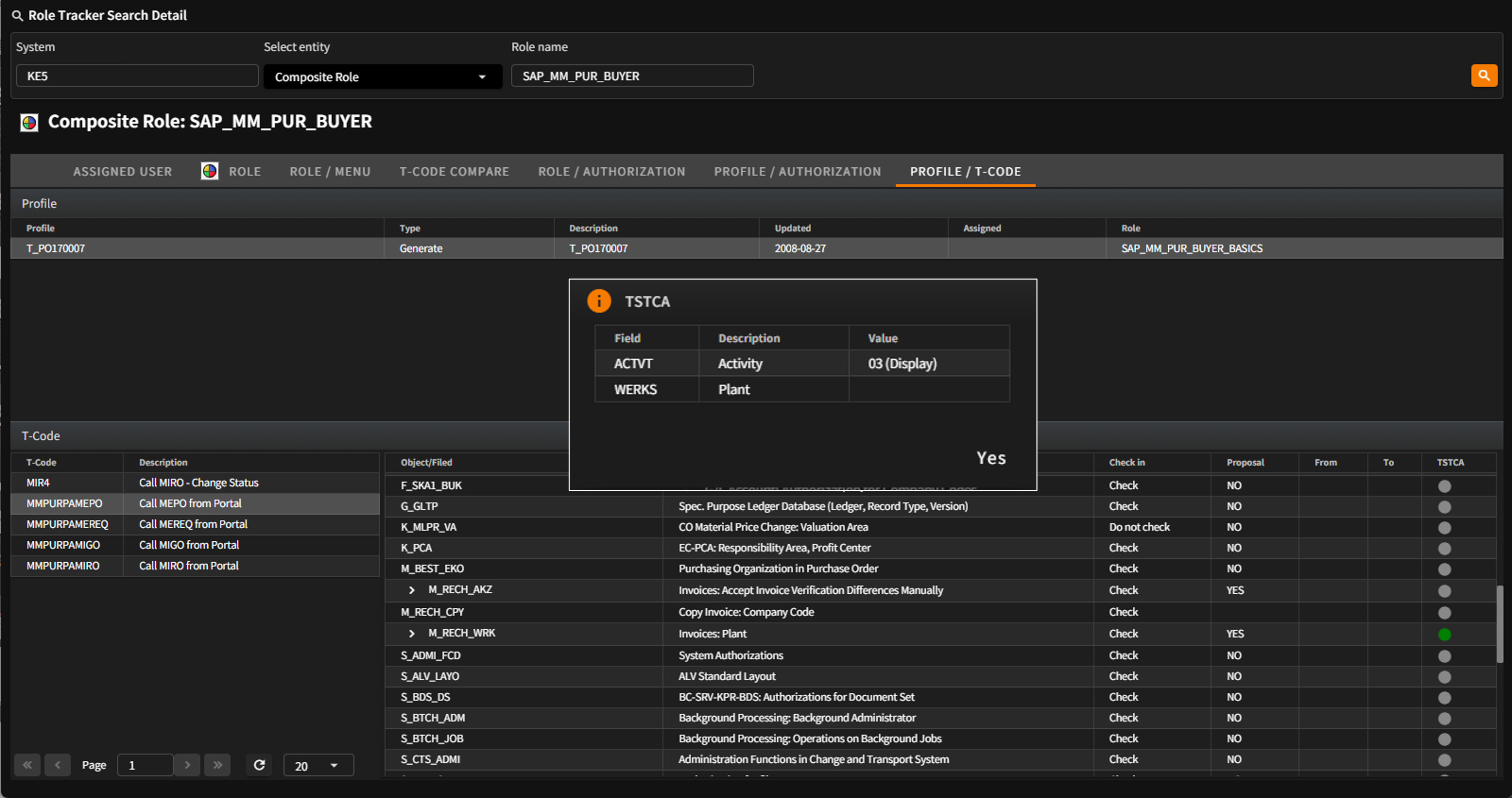
Detailed View of SAP Authorization Objects
- Assigned information
- Related information (User, Role, Profile)
- List of configured T-Codes
- List of configured Authorization values
Detailed Comparison of Authorization Object Settings
- User vs. User (based on T-Code)
- Role vs. Role (based on T-Code)
- T-Code vs. T-Code (based on Authorization values)